API Days - Paris
I travelled to Paris the day before the conference with Matt and we got to the Hotel in the evening, later than expected as we'd not considered traffic when getting a taxi in to Paris from the airport, I think next time I'd probably take the train in. We then met up with Tom and found a local restaurant/bar to have dinner.
As the API Days conference started at 1 o'clock the next day and I was up early I was able to do a bit of sight-seeing before heading back to the hotel to get on with some work and make sure I was ready for my session later that day. I had breakfast and headed out on the metro across Paris to the Eifel tower.
There was a light covering of snow everywhere and it was still very cold and there was more snow coming down as I emerged from the metro, although it didn't really show in the pictures and it was still well before sunrise so everything was quite dark. I grabbed a coffee at one of the nearby cafes and caught up on Slack.
After coffee it had brightened up a bit but was still nice and snowy all around so I walked down closer to the Eifel Tower and a little way along the Seine before heading back across to the Arc De Triomphe and back on the metro back to the hotel. I then made my way over to the Cité des Sciences et de l'Industrie where the conference was to be held. I met Tom as I left the metro station and we headed into the venue together to find the booth and meet the rest of the team.
My workshop "Applying AI to API Testing across the lifecycle" was early in the conference, starting just 30 minutes after the doors opened so I went to get set up fairly early to find that the projector in the room wasn't working but it turned out I'd gone to the wrong room and over in the room I was in everything worked properly. My talk went well and I had some good questions from the audience at the end and was glad to have it done so I could enjoy the remainder of the conference. I spent most of the rest of the day at or around the booth meeting people; discussing API Connect with them; giving demos and guiding them through the sign up for our free 30 day trial.
In the evening of the first day of the conference there was a Speaker Soiree which a few of us headed to after dropping things back to the hotel, it was at Belushi's on the Canal de l'Ourcq so was just a short walk from my hotel. Given the size of the conference and the number of tracks going on the event was packed with those speaking at the event and was a great oppportunity to meet some of the others and share our experiences in the API space. As the world cup game between France and Morocco was on that evening we'd been warned to expect trouble in the streets of Paris, so headed back to the hotel just after half time to avoid anything that kicked off after the match. Later on from the hotel I could hear that France had won with the jubilant sounds of car horns.
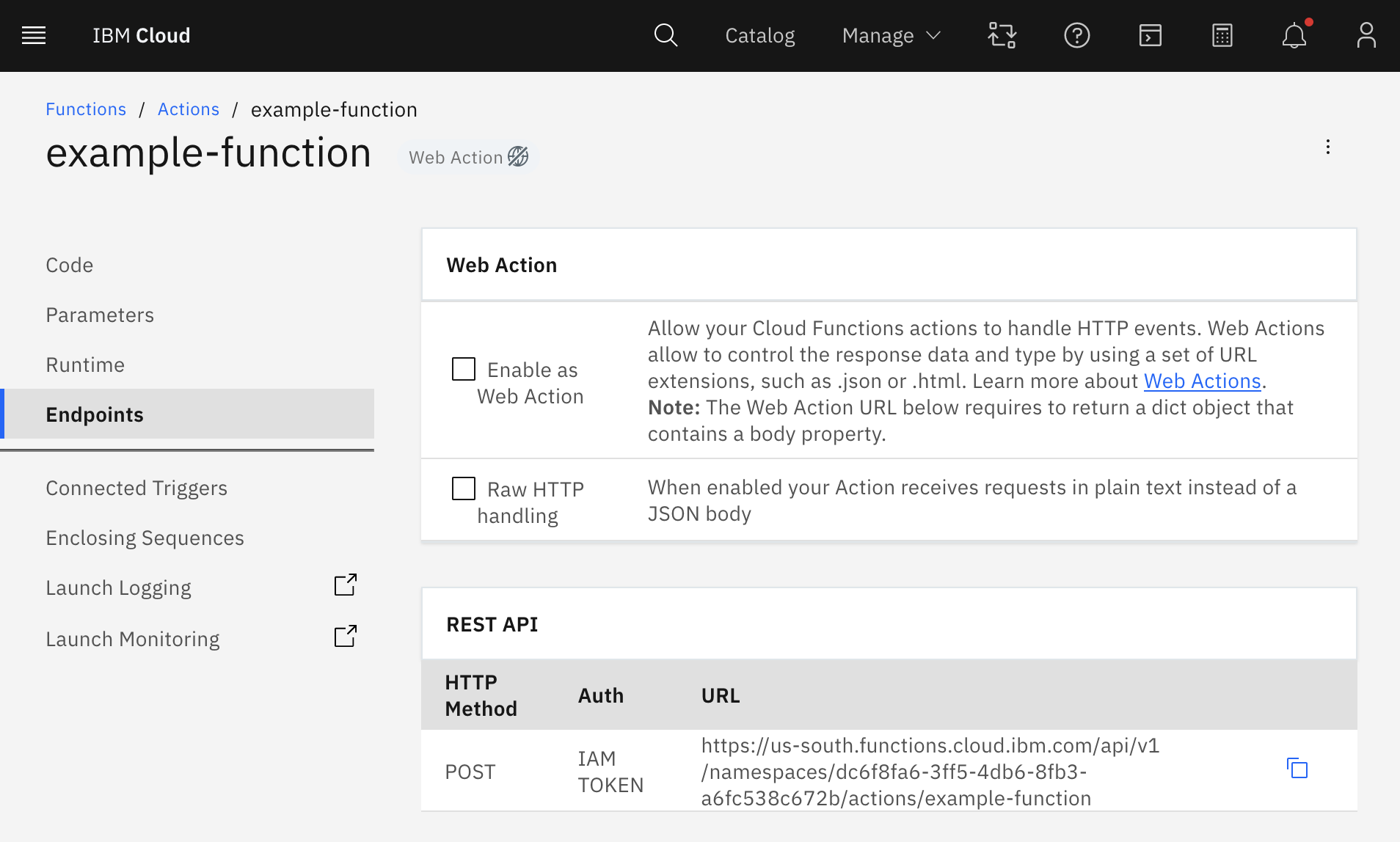
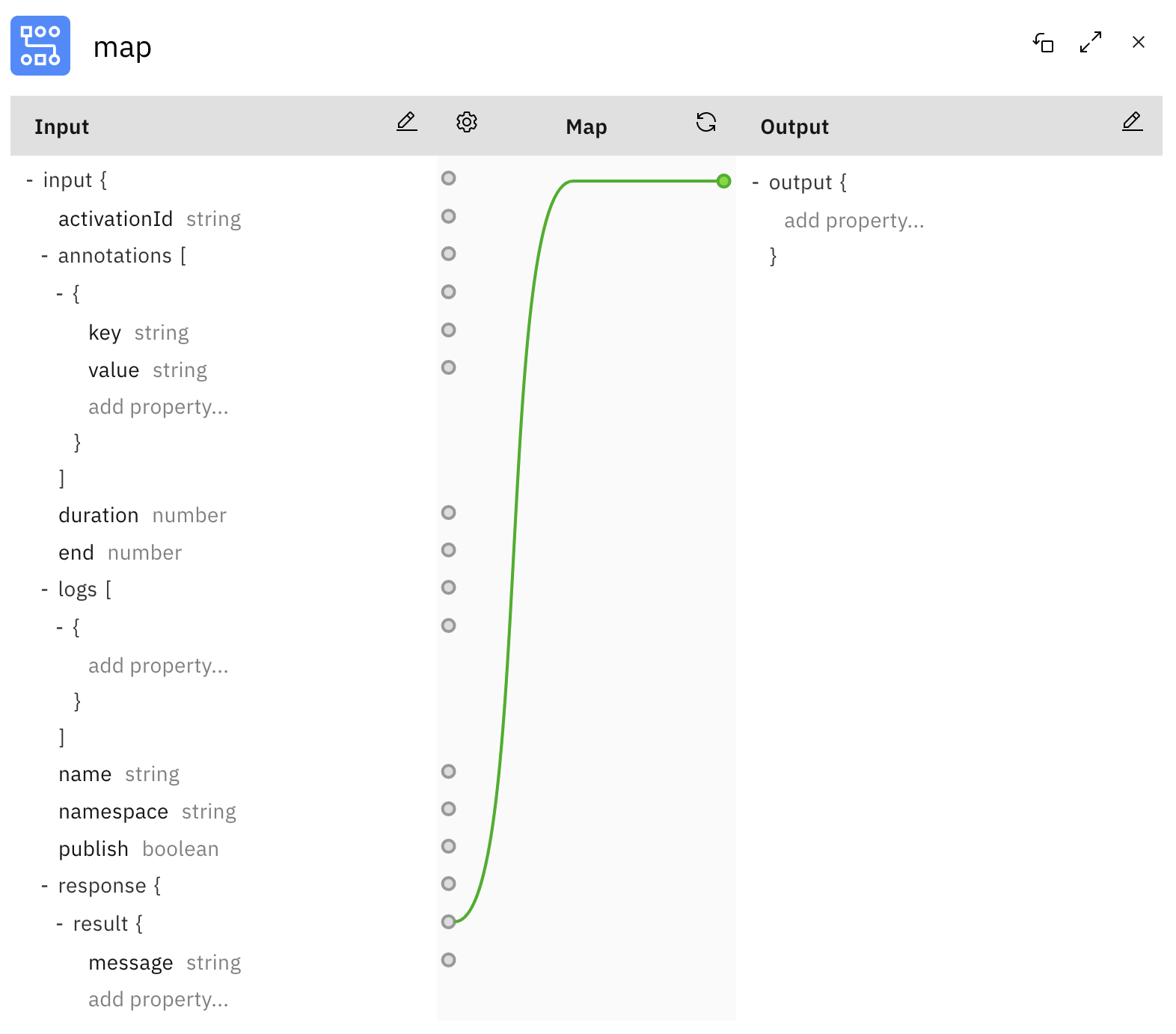
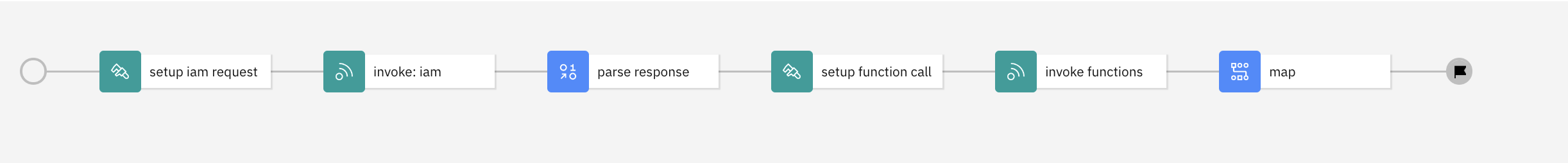
The other thing we had at the booth which was a different idea from the previous time was a series of SmartTalks - 10 minute slots scheduled throughout the event with different people giving a taster session on a topic. I had two on the schedule - "API Deployment automation with IBM API Connect and GitHub Actions" and "Lambda integration in IBM API Connect on AWS". As we were situated by one of the coffee stations we also had a steady stream of people passing our booth so the opportunity to sit down with a coffee and listen to a short talk definitely appealed. These seemed to work really well and drew an audience, often leading to interesting one to one follow on conversations with a few of the attendees.