Blog
New York
The next morning I was up early and decided to head first to the High Line - a park/walkway created from an historic raised rail line which goes along the West Side of Manhatten. It's fantastic to see the way the plants have been selected and seeing trees growing in between the old tracks with different sections having distinct settings from wild prairy to wooded sections providing a relaxed park atmosphere with a unique historic character to it. At the end of the line I headed to the Starbucks Reserve coffee roastery to have a coffee before heading back.
I then went back to my hotel and got changed for the warmer day ahead and headed down to the dock for my boat tour. The boat tour took me right out past the Statue of Liberty with great views across the skyline along the way.
I then checked out the Drama bookshop and then took the subway up to Central Park where I sat in the park to have my lunch.
World Trade Center
Then in the evening I went to Hudson Yards which is a really interesting development built over the top of railway yards, making use of land that couldn't previously be used. There's some really innovative sustainability steps been taken in how water and energy are managed and growing trees in shallow soil encouraging their routes to grow horizontally for stability and nutrients.
Hudson Yards - Sustainability Animation from Neoscape on Vimeo.
I then went up to The Edge where you get stunning views across the city.
The next day was the AWS Summit which was the reason I was in town. This was a massive event and hugely popular, resulting in long queues for attendees to get in snaking across the entrance foyer and around the block. Fortunately being there as an exhibitor I'd been able to arrive early and prepare before the main entrance opened. IBM had a large booth with 4 demo screens and most of the day I spent here meeting people and talking about our new API Connect on AWS SaaS offering. I also got time to explore the other exhibitors and talk to some of the AWS team which was really interesting and useful.
In the evening we had an IBM Client appreciation reception at the classic car club where I met more people and chatted with them surrounded by the impressive car whilst watching the sun go down over the Hudson until it was time for me to head to the airport for my flight home.
Webinar: Launch of new API Connect service on AWS
Garden to Glass
In the afternoon Laura and I did a 'garden to glass' experience at the Hotel, just the two of us, where Diego took us first around the gardens of the hotel to see their sustainability at work and the different plants they grow and how they can be used. We took a basket around with us and gathered lots of sprigs of herbs, flowers and even wild blackberries.
In the gardens we also met Floriana who oversees the gardens at the Belmar who we talked to about natural pest control and composting.
When we got back to the bar, we laid out all the ingredients on a table and Diego showed us how to make a coffee rum cocktail from rum which he'd left coffee beans soaking in earlier - very simple but delicious!
We then got to make our own cocktail from some of the items we'd gathered from the garden - first selecting the spirit and then crushing the leaves together with a caramelised orange segment. We then added these to a shaker with Guaro, syrup and ice and shook it. Diego smoked the glasses on a pine smoker, added ice and then we poured the cocktails in and garnished with more findings from the garden - in this case some flower petals and a carrot leaf.
For the last cocktail we learnt how to garnish the rim of the glass and then could sit back and watch the expert at work in making the cocktails for us with cucumber and basil from the garden.
Selvatura Hanging Bridges
After a delicious breakfast at Belmar, this time I had the breakfast sandwich of pesto, avocado, egg and roast peppers, we were picked up by the Selvatura transport to take us to the hanging bridges tour. We got there early and were assigned to a guide to take us around the park. He took us backwards around in order to avoid the other groups which seemed to work really well! We started the tour with a Coati coming across a mini bridge to us before admiring more of the beautiful cloud forest flora. Then we reached the first bridge of ?, each of which gave us a different view of the forest - some in the trees and some above the trees, all at different heights.
We saw lots more interesting plants and small birds that flew into sight briefly and then off again busy with whatever they were doing in the forest, but also, we saw some that stayed around for us to photograph - such as the Quetzal and Toucanet.
Seeing the forest canopy from above was amazing, so much variety in colours and shapes across the trees it was such a magical place.
After the tour finished, we had a quick look in the shop and lunch in the restaurant - I wouldn't recommend these, just get the transport back.
on to Garden to glass
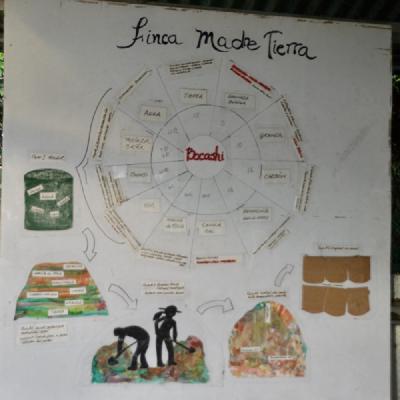
Finca Madre Tierra, Monteverde
Finca Madre Tierra was the first carbon-neutral farm in Costa Rica and we were really excited to visit and learn more about it. We met at reception at 2pm to travel with Oscar, one of the people who run the farm, to travel to the farm, which was about 25 minutes away from the hotel. When we arrived, we were greeted by the farm dogs and the sounds of the animals who after washing our hands we went inside the barn to meet.
First we got to feed the donkeys and then Laura and Abi had a go at milking the cow. Some of the milk was then put into bottles for the young animals and Abi and Jessica fed it to the calves and lambs. The milk from the cows is also used in making cheese for the hotel.
After the animals had been fed, it was time to head outside and learn how to ride the horses. I was first onto my horse and successfully managed to guide it around and over to the water trough, but it wasn't interested in drinking any. We rode for about 45 minutes up and down the stony paths, through the forest and across streams. At one point Oscar stopped and signalled we should all stop behind him as he'd seen a snake - a pit viper in the tree at the side of the path.
We then went back to the barn and had a go at making our own tortillas, which we ate with home-made cheese and eggs from the farm along with aguadulce and farm grown coffee to drink.
After eating we were taken on a walking tour of the farm where we got to see how the farms puts sustainability into action throughout all the different things they produce. We started by visiting the cheese factory where they make the cheese for the hotel from the cows milk. They make the cheese in the mornings, so we got to taste some of the different types of cheeses and see the smoker in action - they burn discarded rice husks to get the smoke, which then are re-used again in the compost mixture they make.
After the cheese we saw the forest to the side of the farm where they've been re-foresting an area and told how they've been working with scientists to study how to get the most effective balance to build a sustainable farming practise. We then went on to visit the coffee plantation, where they grow a particular species of coffee that is best suited to organic growth and less susceptible to coffee
Crushing sugar cane to drink
on to Hanging bridges
Monteverde Cloud Forest Reserve
Early start for a quick breakfast (I had a delicious home-made granola with chia and coconut milk) and then meet our driver at 7am to take us to the Monteverde Cloud Forest Reserve. We had a private guide for the walk around the reserve with whom we saw lots of things and heard lots of birds - nightingale, 'squeaky-door bird (Solitaire), toucanettes and quetzal.
Abi spotted a female Quetzal. The guide was great at showing us everything around on the ground and in the trees and how climate change has affected the area. They used to have only 30 dry days a year and now have 90! 50% of frogs have disappeared with a knock on effect on everything else. I particularly liked the tree ferns, and the tanagers. We also saw a tarantula in its hole.
After the walk around the reserve, we went over to the hummingbird viewing area where they had sugar-water in feeders for the hummingbirds to drink
On the way back we opted to be dropped off in the town of Santa Elena to have a look around and make our own way back to the hotel - it was nice to see, but the walk back was much further than the '15 minutes' we'd been told! We had a juice for lunch and then relaxed for a bit before our trip to the farm we'd booked for the afternoon.
on to Finca Madre Tierra
Zip-lining, Arenal
We started with an early breakfast at 7 with seats right by the front of the restaurant overlooking the volcano watching birds over the water and then headed over to the reception to be picked up at 8:15 for Sky trek.
When we arrived, we put our bags in the lockers and got kitted out with equipment and they gave me a special helmet with a mount for my go-pro so that I could film from there rather than from my chest strap. We were then given the briefing on how to use the equipment and importantly how to brake and were taken up to the stop of the first zip line in the tram.
There were 7 zip lines in all including the longest which was nearly half a mile in length. There were fantastic views from the zip lines overlooking Arenal lake and volcano and it was such a great way to see the area from a different perspective.
After we finished the course we had chips at the restaurant overlooking the volcano and headed back to the hotel for a chilled out afternoon by the pool and finished off the evening in the hotels termales.
Arenal Volcano Hike
This morning we had a relaxing morning in the pool enjoying the swim-up bar and the views across to the volcano whose peak kept peeping out from behind the clouds. We got wood-fired pizzas for lunch by the pool overlooking the volcano and watching wildlife by the lake.
We were picked up after lunch by Canoa Aventura for our volcano hike, which took us along the course of the 1968 lava flows to a view point where we had great views of the volcano and across to the Arenal Lake. The lake is man-made and covers the area to the west of the volcano which was destroyed by soot and gases from the eruption and is used to generate hydro-electric power.
Along the hike we saw lots of epiphytes, in particular bromeliads and orchids such as the One-day orchid (Sobralia sp.), the Spanish flag orchid (Epidendrum radicans) and the endemic Arenal Bromeliad (Pitcaimia Funkiae).
We finished the hike in time to watch the sunset over the lake bathing the volcano in a reddish glow before heading to Eco Termales to bathe in volcanic heated springs under the stars.
on to Zip-lining
Tirimbina - a bonus
Originally our plan had been to fly from Tortuguero to La Fortuna but, due to maintenance issues with the plane, the flight was cancelled and there were no others available. Instead, we travelled by land - initially leaving Laguna Lodge on the boat and travelling by coach to Guapilles and then being picked up by Juan Carlos to take us the rest of the way. This meant that we were able to stop off at Tirimbina on the way where we had a guide, Luis, to take us around the reserve.
The tour took us across a hanging bridge into the primary forest and around a circular path through the forest, along which we saw interesting plants and animals.
Some of the highlights were the views into the trees from the hanging bridge, the walking palm with nibbed roots and the closer view of a sloth.
on to Arenal - Volcano Hike
Exploring Tortuguero
We started the day with an early wake up (not too hard as we weren't adapted to the timezone yet) at 5am for coffee before an early morning boat tour leaving at 5:30 and taking us around the riverbanks and into the park spotting wildlife. The tour started with the local banks just up from the hotel where we started off with an Iguana lounging on a branch of a tree, just a little way up from a Tiger Heron (Tigrisoma fasciatum). José pointed out the different stages of coconuts growing along the side of the river as they go from green with mostly milk to brown with mostly flesh, we then saw a solitary howler monkey or 'mono congo' (Alouatta palliata).
We then headed down into the national park, stopping briefly for José to provide our ticket reference numbers at the ranger's office to confirm we could all enter the park. As we passed through the parks more vibrant canals, we saw a number of birds including herons, cormorants and then noticed all the tour boats gathered in a circle around something in the water. We joined the circle and then realised what they were watching - dolphins! We continued to watch them for a while - could see a group of them with young, but I didn't manage to time it right to capture a photo of them - was amazing seeing them making their way along the river breaching the surface in their group.
After following the dolphins for a while, we then headed back down the river and heard the sounds of a group of Howler Monkeys and then saw them including a mother with a baby on its back swinging through the trees.
After this we went back to the hotel for breakfast and to decide if we went on the next boat tour as well or not - I decided to go whilst the others stayed and enjoyed the hotel pool. It poured with rain whilst on the tour - thankfully I was wearing the provided poncho, but the rain still seemed to get everywhere! I also managed to see some more wildlife and get some better photos.
It was particularly amazing to see a sloth asleep in the tree just across the river from the hotel, and to see a Basilisk in a different colour (as they change colour)
On this tour we went a slightly different route through the park, into some of the smaller waterways and so saw different wildlife - such as the Caiman and the bats
After lunch we had a walking tour around the gardens of the hotel where we saw a surprising number of things just around the hotel grounds. Some of the highlights were the banana flowers, the hanging nests of Montezuma Oropendola birds, the Green Macaws and the Iguana that was relaxing in the bushes metres away from our rooms!
The last adventure of the day was an evening tree-frog hunt in the trees around the swimming pool by torch light. We managed to see two different tree frogs high in the leaves.
on to Tirimbina
Travel to Laguna Lodge, Tortuguero
After an overnight stay in San José, the next part of our travels began with a coach to the docks at La Pavona, followed by a boat from there to Laguna Lodge, as Tortuguero can only be accessed by boat or plane.
We set off from Hotel Presidente at 6:10 after a quick bite for breakfast. José, our guide, had met us at the hotel and took us to meet the bus with the others who were travelling to Tortuguero. After a couple more pickups we headed out of San José along the route 32 heading higher up as we left the city, passing alongside coffee plantations.
We then headed through the cloud forest of Braulio Carrillo National Park and passed over the continental divide between the Pacific and Caribbean sides of Costa Rica. Along the way, José provided a commentary for us about everything we were passing in both English and Spanish, which was really interesting and a great way to get tuned into the language. Some of the highlights were the indicative species of a cloud forest - known locally as the poor man’s umbrella (Gunnera insignis), the dark colour of the Rio Sucio as it picks up the oxides on it's route from the Irazu volcano.
We stopped a breakfast of Palmitos and rice at Rio Blanco restaurant in Guapilles where we also got to explore along by the river. As we returned to the coach, José asked us if we'd seen the frog and as we hadn't, he took us back to see it and scooped up the poison-dart frog from the undergrowth to place on a leaf for us to see clearly. After lunch, we passed through banana plantations complete with their own banana train to transport bananas which we had to stop for while the bananas crossed the road.
When we got to La Pavona, it was interesting to see all the boats waiting at the docks and the supply boat being loaded up with lots of bags of rice!
From there we boarded the boat to head along the windy river to the lodge. Along the way we had our first insight to what was in store for us in the park - passing through jungle landscapes and seeing monkeys, lizards and birds. Our lodges were side by side just around the corner from the botanical garden walk and the path through to the beach on the Caribbean side, which is where the sea turtles' nest and bury their eggs.
We had lunch at Laguna lodge and in the afternoon visited the town of Tortuguero by boat. Tortuguero is a very small town with a number of shops and cafes and we were able to stock up on insect repellent and buy some post cards and souvenirs, however as there is no postal service there we couldn't get any stamps. When we got back me and Jessica explored the botanical garden and saw a hummingbird, a blue morpho butterfly, a snake and lots of interesting plants.
on to Exploring Tortuguero